What to do if someone has my IP address? If you feel you have been hacked, this guide shows you what you should do right now to protect yourself. We won’t go deep on the reasons behind these actions, but we have many articles to go deep down after you fix the problem. Now, the priority is to limit the damage and contain the security breach.
What to do if someone has my IP address? Here’s the answer:
- Check if it is true
- Change your IP
- Assess potential damage
- Understand how they got it
We can now explain each topic in much more detail.
What To Do if Someone has my IP Address?
1. Check If It is True
Know that it is probably true, because getting someone’s IP address is easy online. Nonetheless, if you think someone has your IP address you must verify if they are telling the truth. If you can talk with this person, say that you don’t believe them and to give you the IP address to show they are not just talking.
The IP address is a combination of 4 numbers ranging from 0 to 255 separated by dots, for example 43.127.255.36 may be a valid IP address. To check yours’, you need to go to a website such as whatsmyip.org. They will tell you plain and simple what is your IP, like we see below.
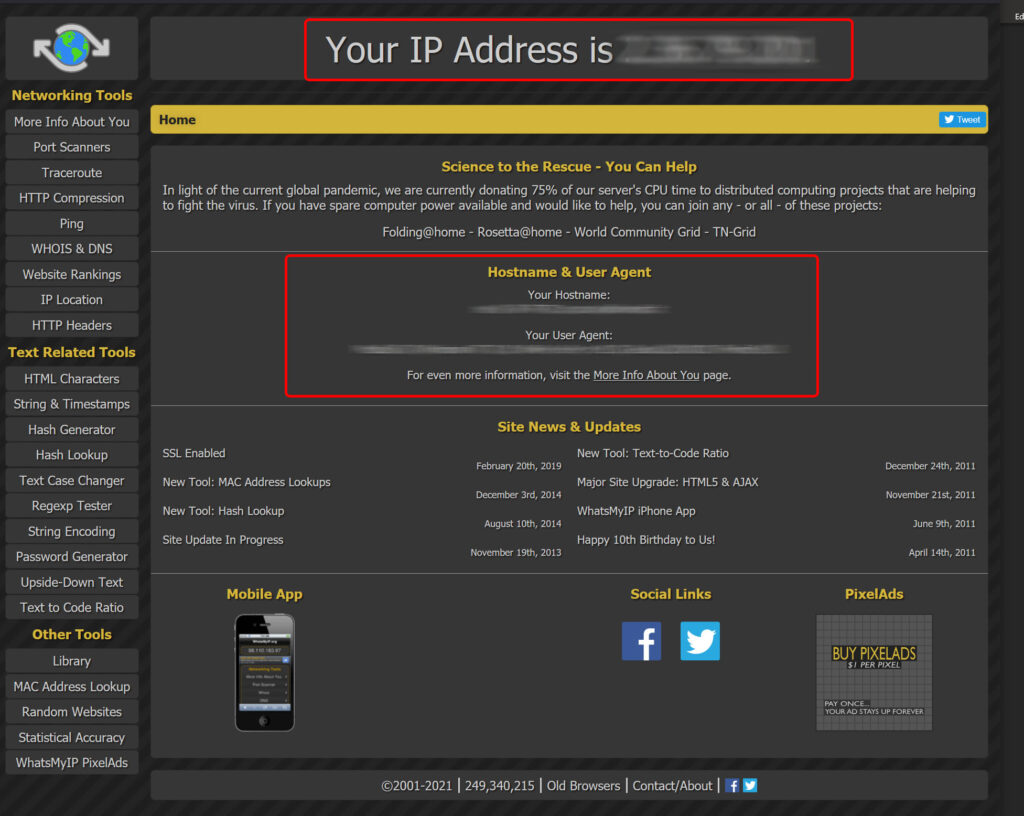
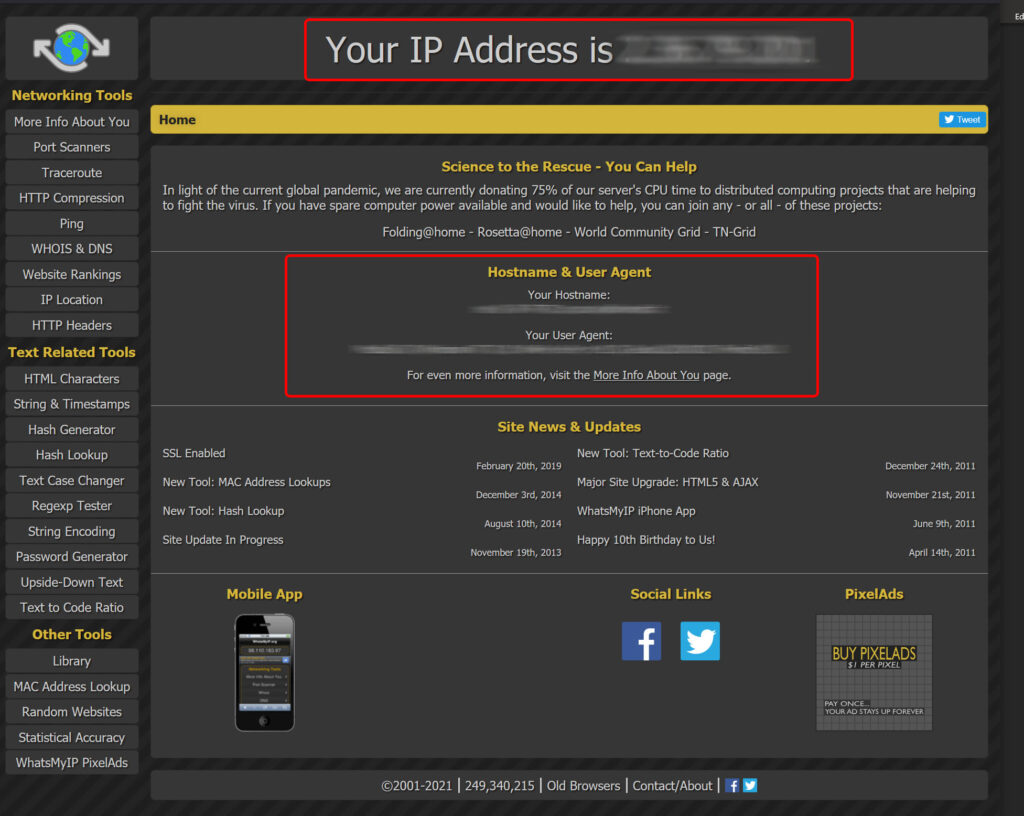
You should look for your IP at the top, as well as some additional information regarding your hostname and user agent (that is, your browser, the app you use to access the Internet). All these information can be easily retrieved from anyone who is tech savvy enough.
Remember that IP address is related to the network connection to the Internet. If you use a Wi-Fi connection and a cellular network, you need to access What’s My IP from both, because you will have a different IP on each, and then check which one of the two the hacker possess.
Never reply to SPAM emails from unknown sender. Is someone claims they have your IP address in an email from someone you never communicated with, do not reply. Spammer send thousands of emails to random addresses and see who is fool enough to reply: if you reply, they will start to target you actively. If someone in an email claims they have your IP address and they provide it to you, check it. If not, just assume they have it: better be safe than sorry.
Also beware of replying to emails that seem sent by yourself. They are not, it is a SPAM trick not all email providers prevent.
2. Change Your IP
What to do if someone has my IP address? Long story short, change your IP address. In this way, the information they possess becomes worthless. Of course, if you are sure they are just faking it and they do not know your IP address, then there is no need. Instead, if you know they really have it, or if you cannot verify it (because it is a SPAM email), just change your IP.
Changing your IP can be done quite simply, depending on where you are connected.
- On a home Wi-Fi, just reboot or power cycle the router. If that does not work, try to keep it powered off for the night or for 24 hours
- On a mobile network, shutdown data connection and Wi-Fi connection and remove reboot the phone
- If you are on a public Wi-Fi such as an airport or coffee shop, just disconnect and do not reconnect
- If you are on an office Wi-Fi, you might be out of lack because IP address is often static, particularly in large companies. You should contact your IT or Information Security department immediately
Sometimes, the IP address assigned to your network is static. This is something you request to your provider, so for most people this won’t be the case. If it is, then you can either ask your provider to change your IP, but if you wanted it to be static you had a reason, and it may not be possible to change. You will need to learn to live with the idea that someone has your IP address (more on this later).
3. Assess Potential Damage
Even if you changed your IP, the hacker had your IP address for some time (from the time they got it, to the time you change it). In other cases discussed previously, you may not be able to change your IP at all. So, it is important to know what the hacker can do with your IP, or what they might have done.
What the hacker can do depends on your network setup, and there are two main camps. On one side, we have the traditional home network. This is a technology called NAT Overload, and it is what most homes and also service providers use for consumer phones. If this is your case, which most likely is, then they cannot do much to you.
On the other camp, we have networks that expose services toward the Internet. This is different from NAT overload, because with NAT Overload you only consume content, and you are in charge. If you want to go to Netflix, or Amazon, or whatever, it is you to decide to do so. Instead, with exposed services you are just making something available on the Internet, for everyone to reach. Common examples of this are:
- VPN network to your home or office
- A NAS published over the Internet (e.g., Synology, QNAP and similar)
- Videoconference endpoint published over the internet with some protocol such as H.323
- Web server made reachable to others online
- A game server for an online game made reachable online
- Virtual Private LAN such as LogMeIn Hamachi
You are a network exposing an IP over the internet if it is your network exposing that IP, not if you are reaching for example a game server in someone’s else network.
If you are exposing something over the Internet, you really need to do a deep check to understand what you are exposing exactly, and what are its vulnerabilities. Here, what the hacker can do depend on what you are exposing, what is its hardware and software version, and what are its bugs and vulnerabilities. A hacker can exploit any published vulnerability, so it is important that you check them and try to remediate.
This requires technical expertise, doing things like checking CVEs vulnerabilities. If you don’t know how to do it, you can either call a professional or just unplug everything from the network for a while.
4. Understand How They Got It
What to do if someone has my IP address? Ensure it doesn’t happen again! To do that, you need to realize how they got it in the first place. Unfortunately, getting someone IP address online is easy: you just need to interact with them over the Internet, such as browsing their website or having a Zoom call with them.
To understand how a hacker might have got your IP address, you have to dig deep into your past activities. If your IP is not static in a week or so, hence there is a one-week window for the hacker to get your IP. You need to go backward and trace all your online behavior during that period. Do this:
- Read your browser history line by line, site by site, looking for websites that might look “strange”, with names you don’t know, or that you might think “I didn’t realize I was visiting this”
- Try to remember any website you accessed with incognito mode and that will not be visible on your browser history because of that.
- Reconstruct your history of calls with any videoconferencing application: Zoom, Skype, Microsoft Teams, Google Meets, and similar.
- Reconstruct your history of online gaming behavior, such as games played, and other apps used such as Discord or Twitch.
- Check what apps and software you downloaded recently.
- Check any email you received that included images in the body, links, or attachments.
For everything, you should try to have a detailed chronology, ideally with day, hour, and minute of each activity. This is crucial, and can be helpful if things get serious and go onto a legal ground and you want your ISP to fetch some data for you. Once you have reconstructed everything that happened, look for something that doesn’t feel right, for example a website you didn’t know you visited, and try to see what happened.
For example, check the websites you visited immediately before or immediately after. It may be they had some redirect to a malicious website that lasted less than a second (common in not-so-legit websites).
What To Do if Someone has my IP Address, in short?
Disconnect, unplug from the Internet for a while. Even if they don’t, realize you are not necessarily in danger and things might turn out just fine. If you follow the 4 steps of this guide, most likely you will be fine:
- Check if it is true
- Change your IP
- Assess potential damage
- Understand how they got it
If all of this does not satisfy you, you can always hire a cybersecurity professional to protect our online image. Now, if you are curious, you can see this from the other side: how hackers can get your IP address so easily.
Remember, as always, that is not meant to be a comprehensive guide on how to protect yourself, but just some common-sense best practices. If even in spite of these actions a hacker is able to cause you damage, we cannot be held liable. We provide information with an educational purpose, and information is provided “as is”.
